Wiz AI-APP Launch — Audited.
Introducing Wiz AI Application Protection Platform (AI-APP)
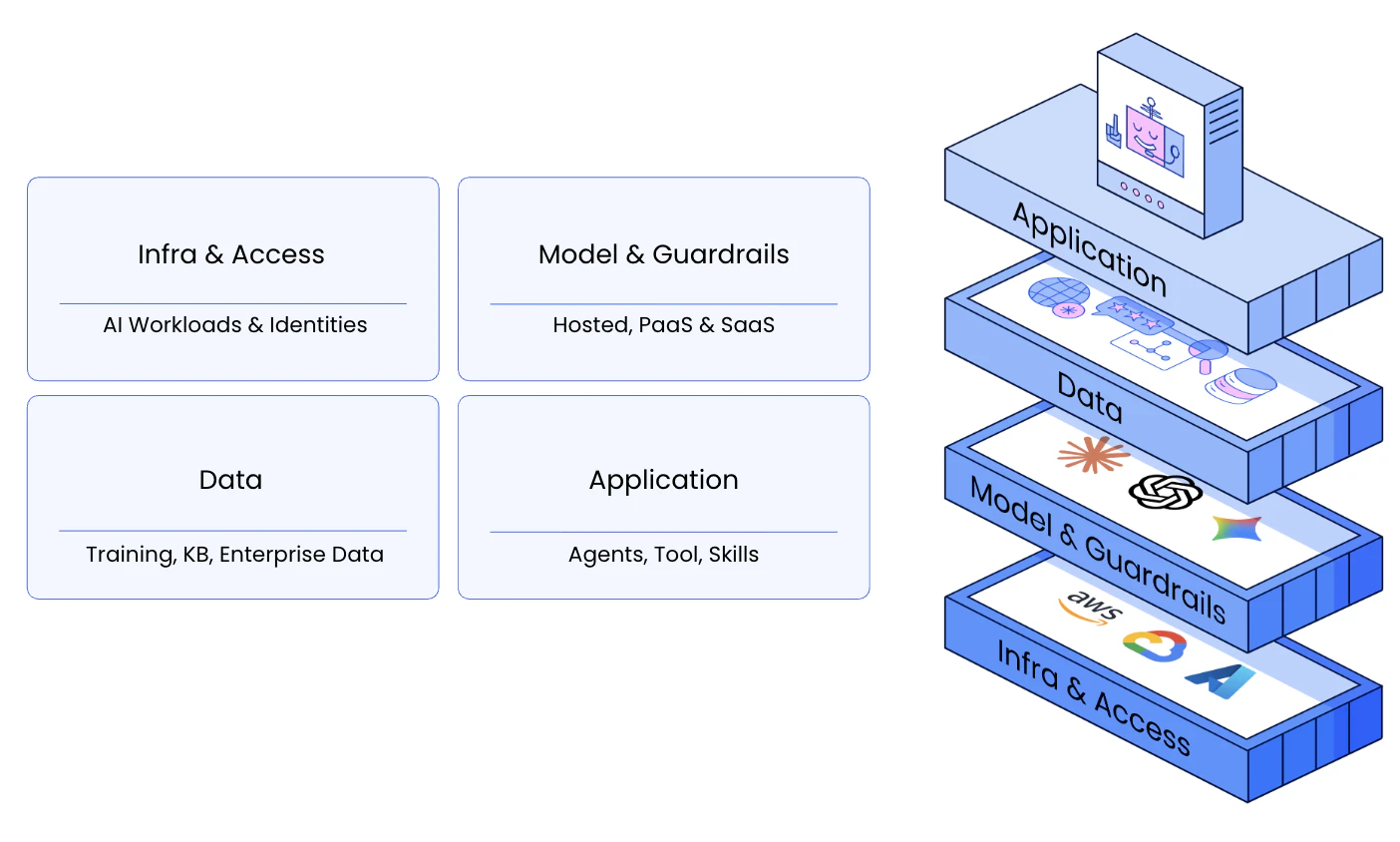
AI hasn't just changed how we build — it has fundamentally changed how risk emerges. AI applications are dynamic, interconnected systems combining models, agents, tools, data, and infrastructure across code, cloud, and runtime. Most approaches still analyze infrastructure, identity, and applications in isolation — leaving teams without the context needed to identify real risk.
Today, we're introducing the Wiz AI Application Protection Platform (AI-APP) — designed to secure AI applications end-to-end, with the context needed to understand real risk and act on it.
The Context Gap in AI Security
Security teams are left trying to answer:
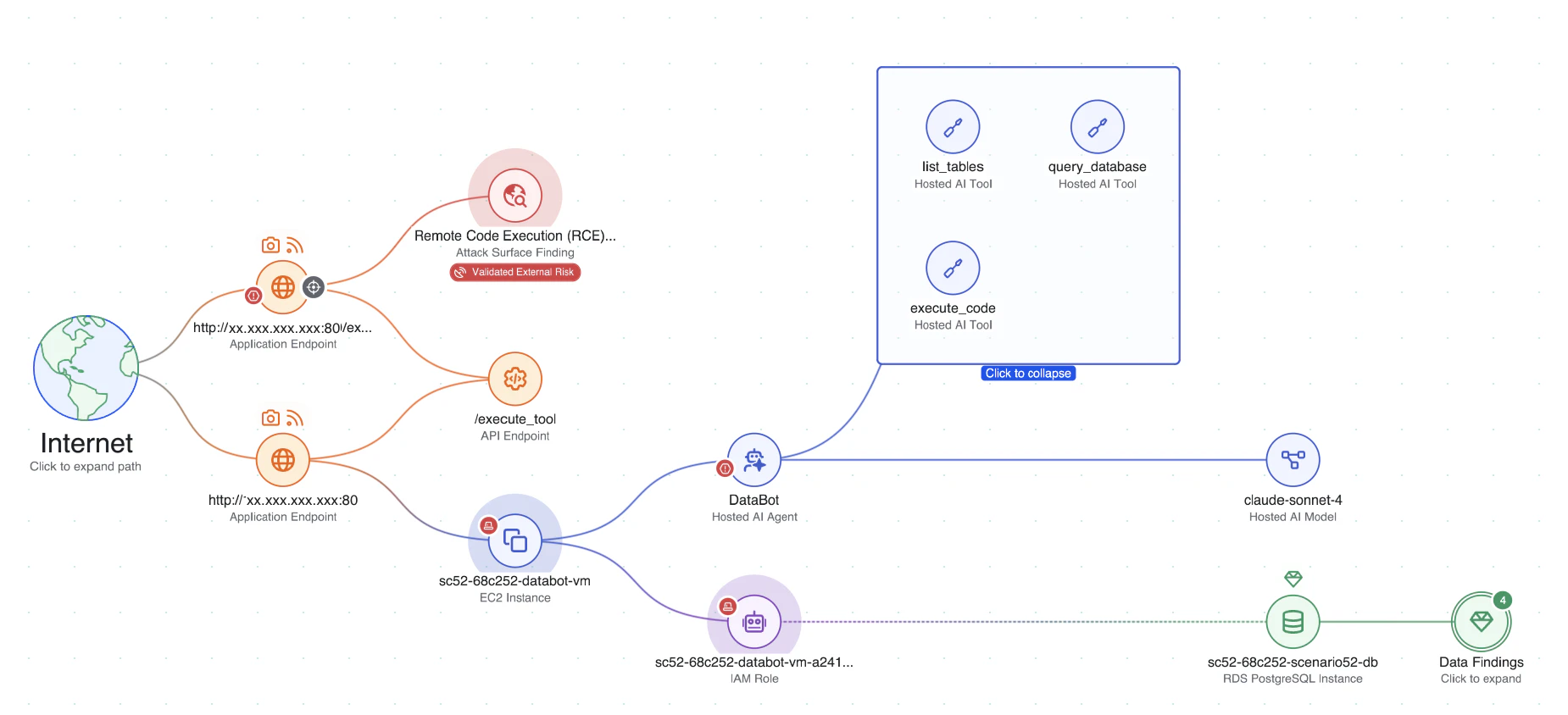
Consider a customer-facing AI chatbot connected to internal tools and data systems. An attacker discovers an authentication bypass vulnerability — a common issue in rapidly built, "vibe-coded" applications — and uses it to inject a prompt, manipulating the agent into taking unintended action.
1. Visibility — Build a Complete AI Inventory
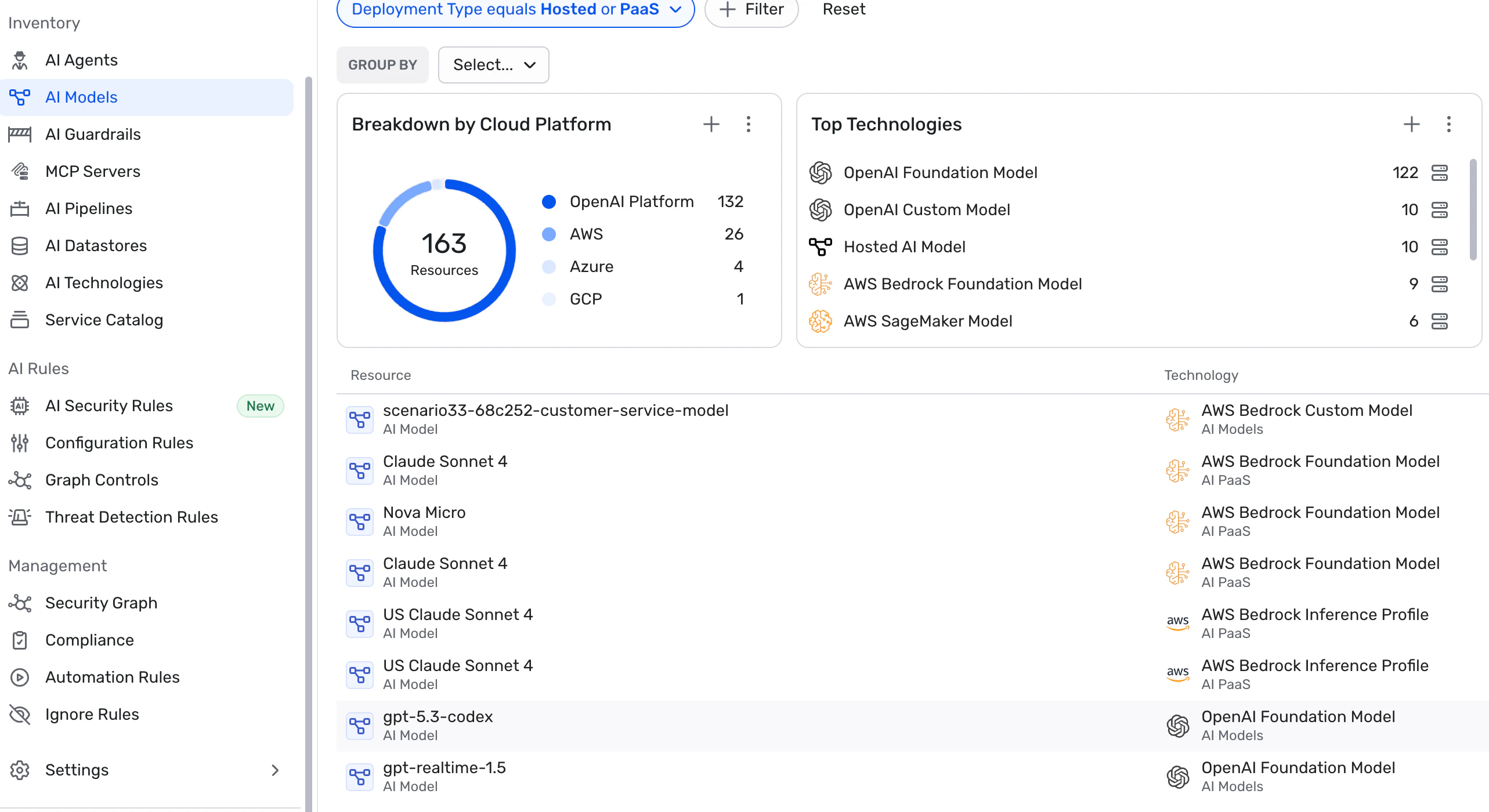
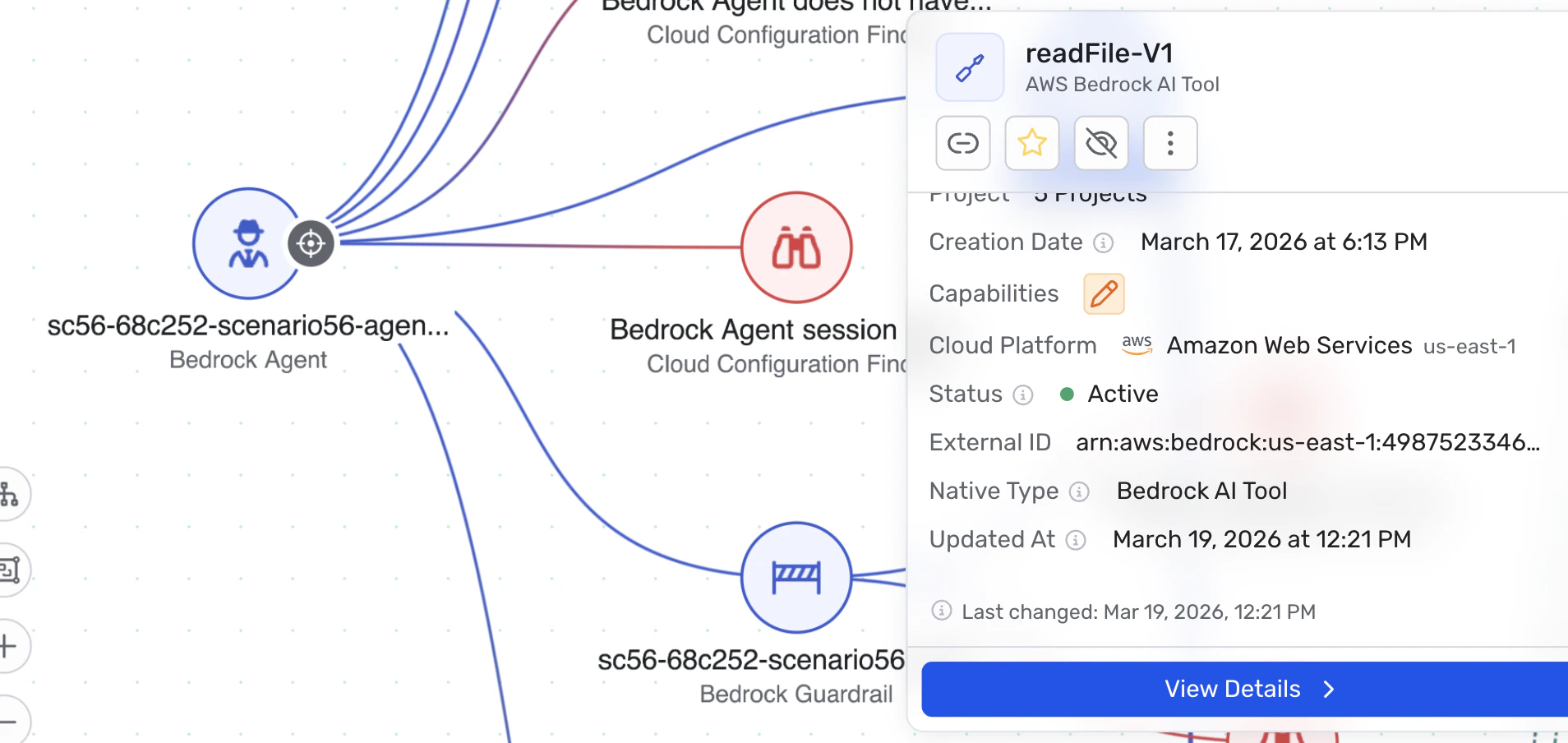
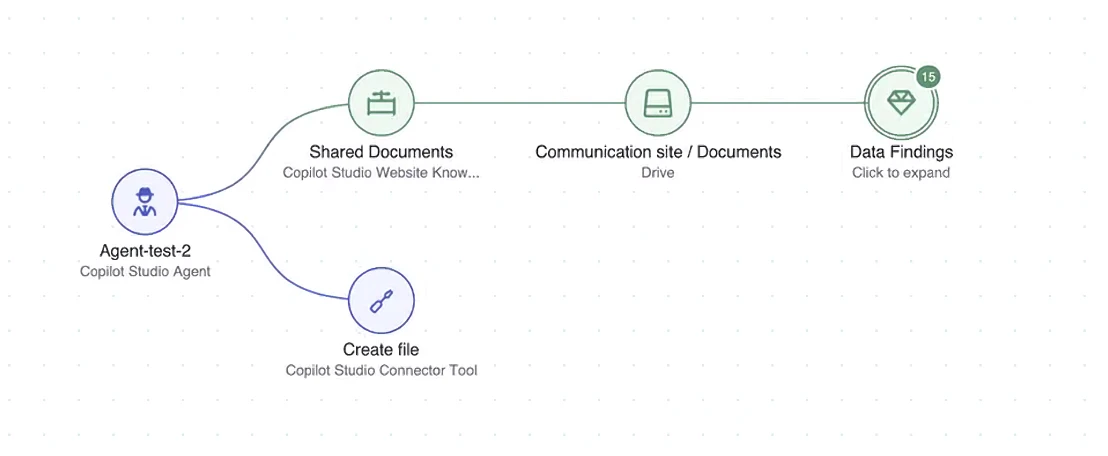
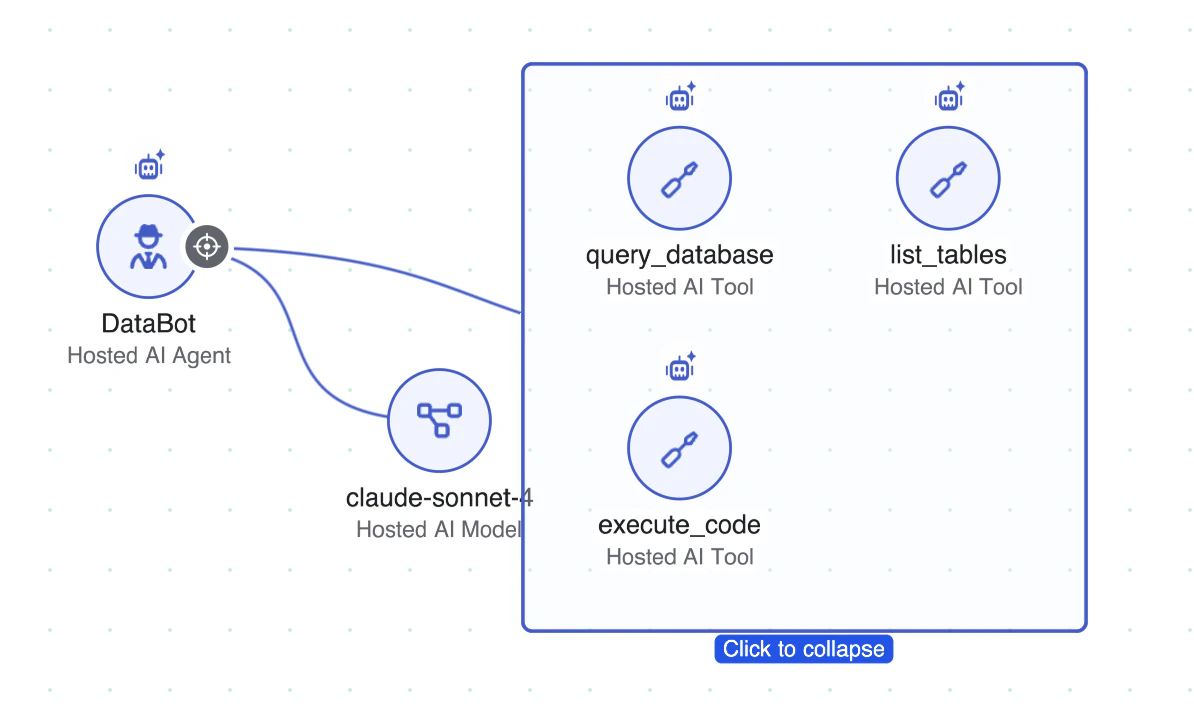
Wiz builds a complete inventory of AI applications using multiple detection methods:
2. Risk — Understand How Risk Emerges Across Layers
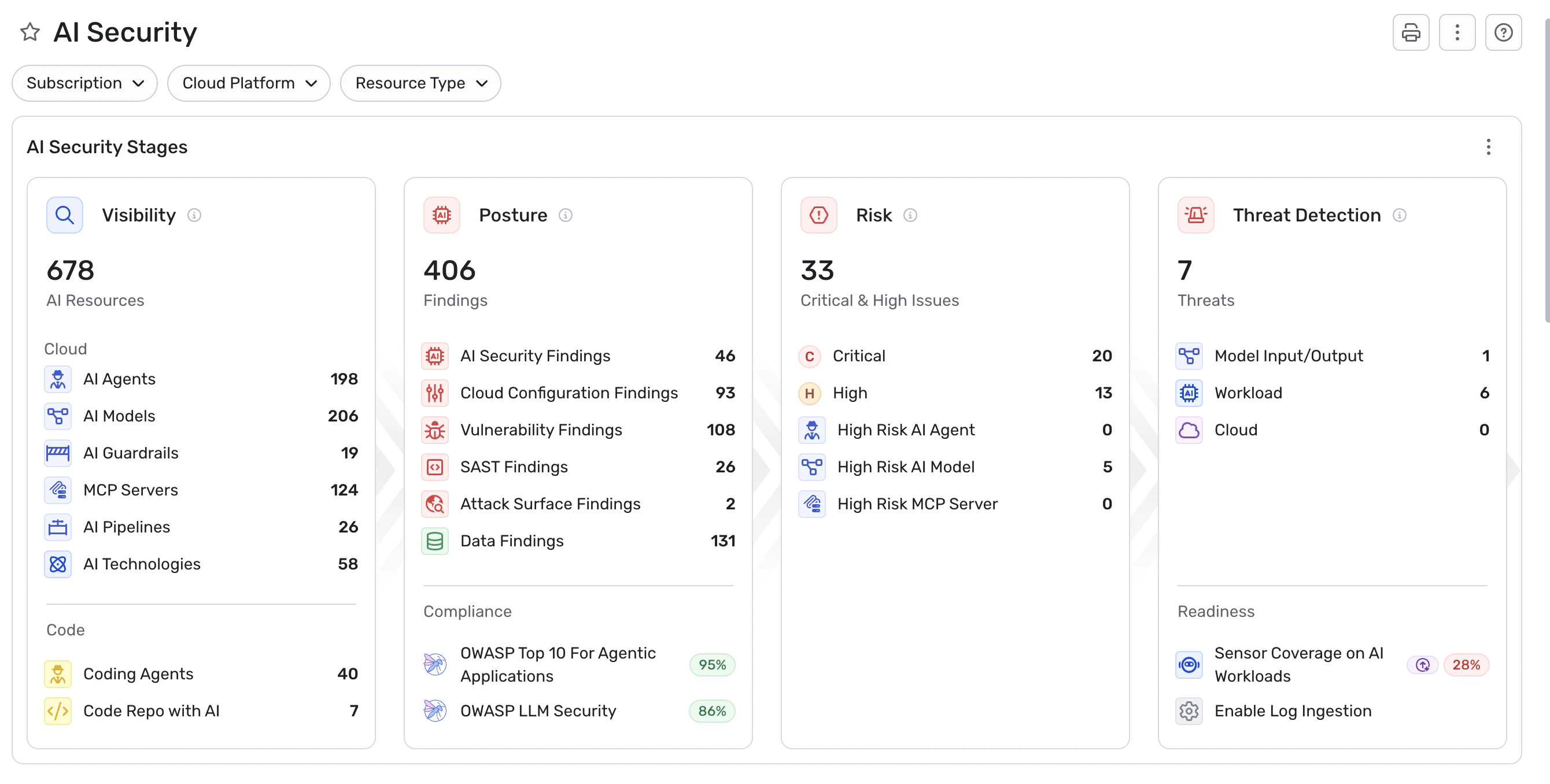
AI risk doesn't live in a single layer. It emerges when systems interact — across models, agents, tools, infrastructure, and data. The platform brings together visibility, risk analysis, and runtime protection into a single, graph-powered platform.